en
TRINETRA-360
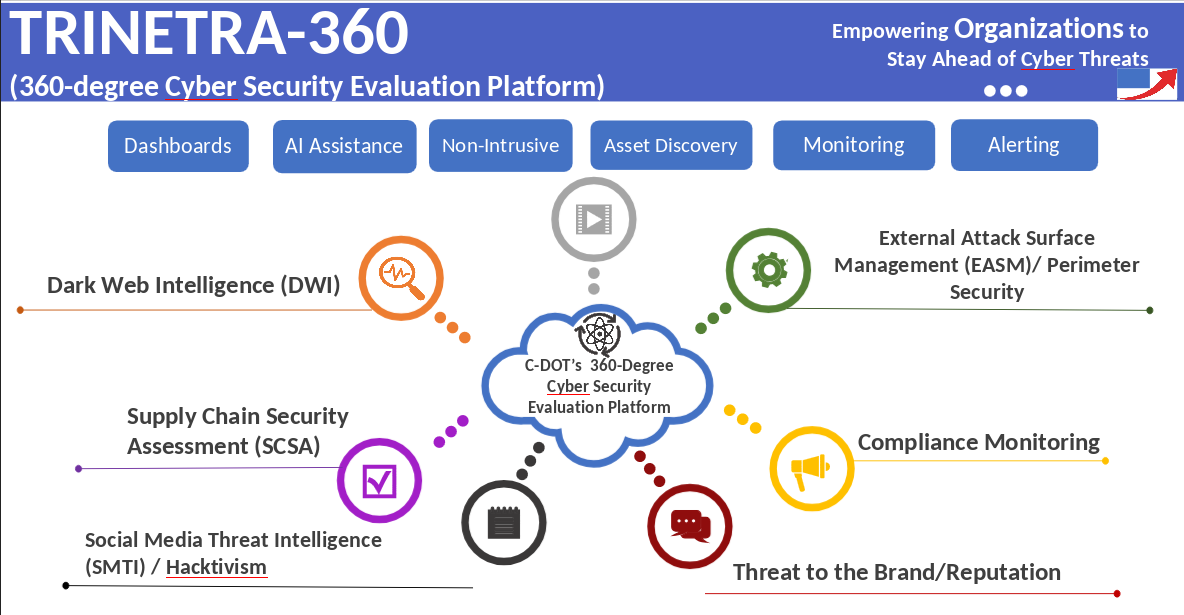
C-DOT’s TRINETRA-360 is Cloud-Based, AI-powered, Outside-In based Cybersecurity Evaluation platform which provides the 360-degree view of Cyber Resilience of an Organization’s external-facing digital assets and security defences with 360-degree coverage without even penetrating anything into the Organization. Assessment by TRINETRA-360 focuses on identifying risks that external attackers could exploit, ensuring potential security gaps are addressed before they lead to breaches. Non-intrusive scanning and External Attack Surface Management (EASM) are well- established approaches that analyses an organization's public-facing assets to find vulnerabilities without actively probing or disrupting the network. The inclusion of Dark Web monitoring, Brand Monitoring and Cyber Intelligence is crucial for proactive de- fence, as they can detect leaked credentials, phishing sites, fake mobile applications, stolen data, and planned attacks before they are executed.
- Perimeter Security / External Attack Surface Management (EASM):Provides continuous outside-in visibility to identify exposed vulnerabilities and potential attack vectors across the organization’s perimeter before they can be exploited, strengthening the overall security posture and reducing risk.
- Compliance Monitoring:Assesses security against industry and regulatory standards. It is a continuous process that provides a real-time view of an organization’s security posture, helping detect and address potential violations before they lead to a security incident.
- Supply Chain Risk Management (SCRM):Evaluates and scores security risks posed by third-party vendors, helping organizations understand and manage risks introduced through their supply chain ecosystem.
- Brand Monitoring:Detects indicators of indirect attacks that often occur outside the organization’s direct network perimeter, such as fake websites, typosquatted domains, or malicious mobile applications impersonating the brand.
- Social Media Threat Intelligence (SMTI) / Hacktivism:Identifies threats, vulnerabilities, and potential hacktivist activities across social media platforms, making it a crucial component of a modern cybersecurity strategy.
- Dark Web Intelligence (DWI):Detects hidden risks, exposed credentials, and potential data leaks circulating on the dark web, enabling organizations to take proactive security measures.
- Cyber Intelligence:Provides actionable insights to help organizations understand emerging cyber threats, attacker tactics, and evolving risk landscapes.
- Perimeter Security / External Attack Surface Management (EASM):Provides continuous outside-in visibility to identify exposed vulnerabilities and potential attack vectors across the organization’s perimeter before they can be exploited, strengthening the overall security posture and reducing risk.
- Compliance Monitoring:Assesses security against industry and regulatory standards. It is a continuous process that provides a real-time view of an organization’s security posture, helping detect and address potential violations before they lead to a security incident.
- Supply Chain Risk Management (SCRM):Evaluates and scores security risks posed by third-party vendors, helping organizations understand and manage risks introduced through their supply chain ecosystem.
- Brand Monitoring:Detects indicators of indirect attacks that often occur outside the organization’s direct network perimeter, such as fake websites, typosquatted domains, or malicious mobile applications impersonating the brand.
- Social Media Threat Intelligence (SMTI) / Hacktivism:Identifies threats, vulnerabilities, and potential hacktivist activities across social media platforms, making it a crucial component of a modern cybersecurity strategy.
- Dark Web Intelligence (DWI):Detects hidden risks, exposed credentials, and potential data leaks circulating on the dark web, enabling organizations to take proactive security measures.
- Cyber Intelligence:Provides actionable insights to help organizations understand emerging cyber threats, attacker tactics, and evolving risk landscapes.
- User Interface: Web-based dashboard that provides centralized access to security insights, risk scores, alerts, and monitoring results through an intuitive and user-friendly interface.
- Holistic Risk Assessment:
Gain a comprehensive 360-degree view of your organization’s cyber resilience, enabling better visibility into potential risks and security gaps. - Proactive Threat Detection:
Identify risks in a non-intrusive manner before they escalate into security breaches, allowing organizations to take preventive action. - Prioritized Risk Management:
Focus limited security resources on the most critical and likely threats, ensuring efficient and effective risk mitigation. - Continuous Security Improvement:
Leverage continuous monitoring, feedback, and analytics to strengthen defenses and stay ahead of the constantly evolving threat landscape. - Automatic Active Asset Discovery:
Automatically discovers active digital assets across the organization and scales seamlessly as the organization grows.